LESS NOISE
-80% ALERT VOLUME
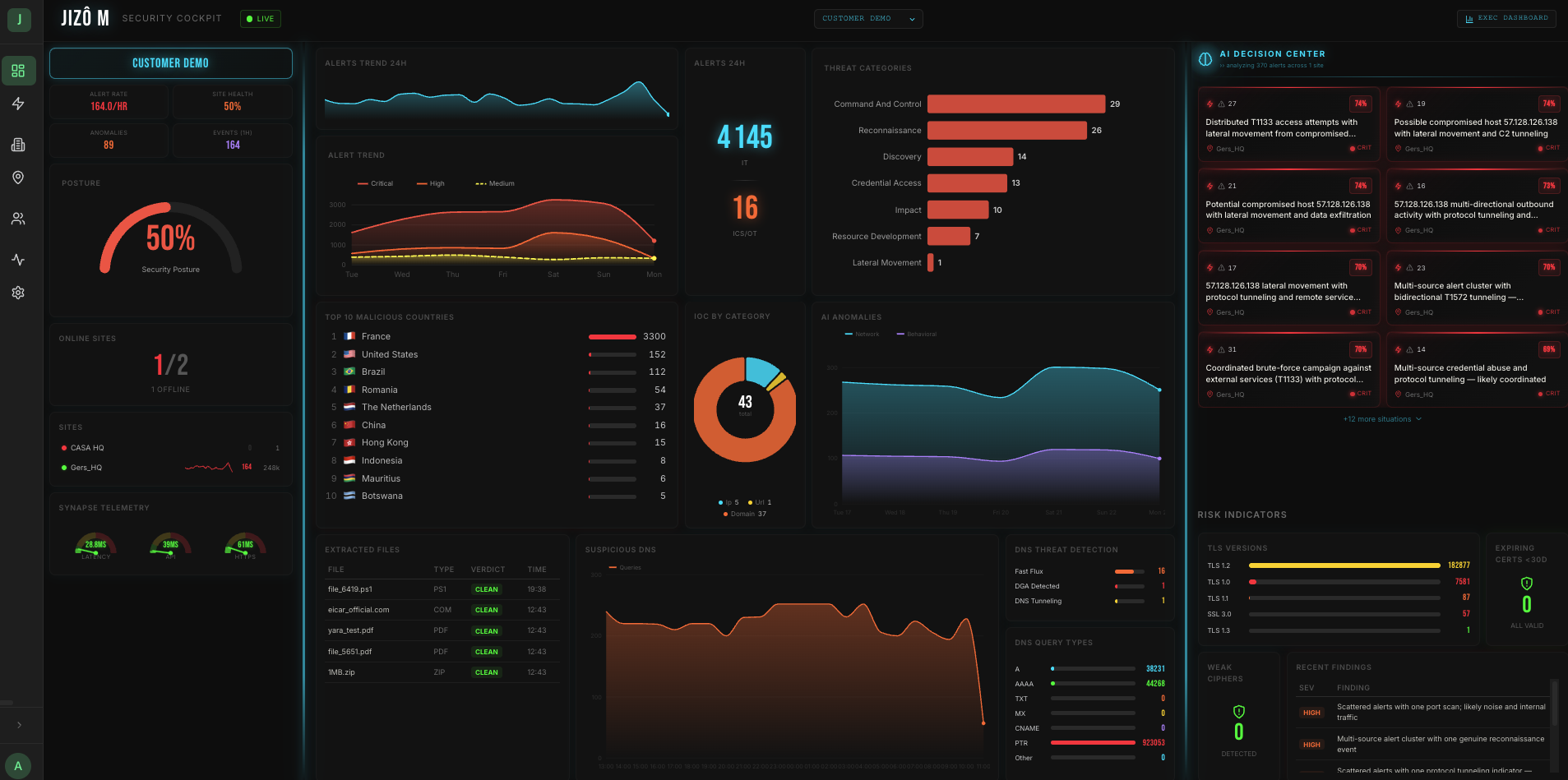
Incoming signals are automatically aggregated and correlated. Analysts work the queue that matters.
Cyber Threat Detection
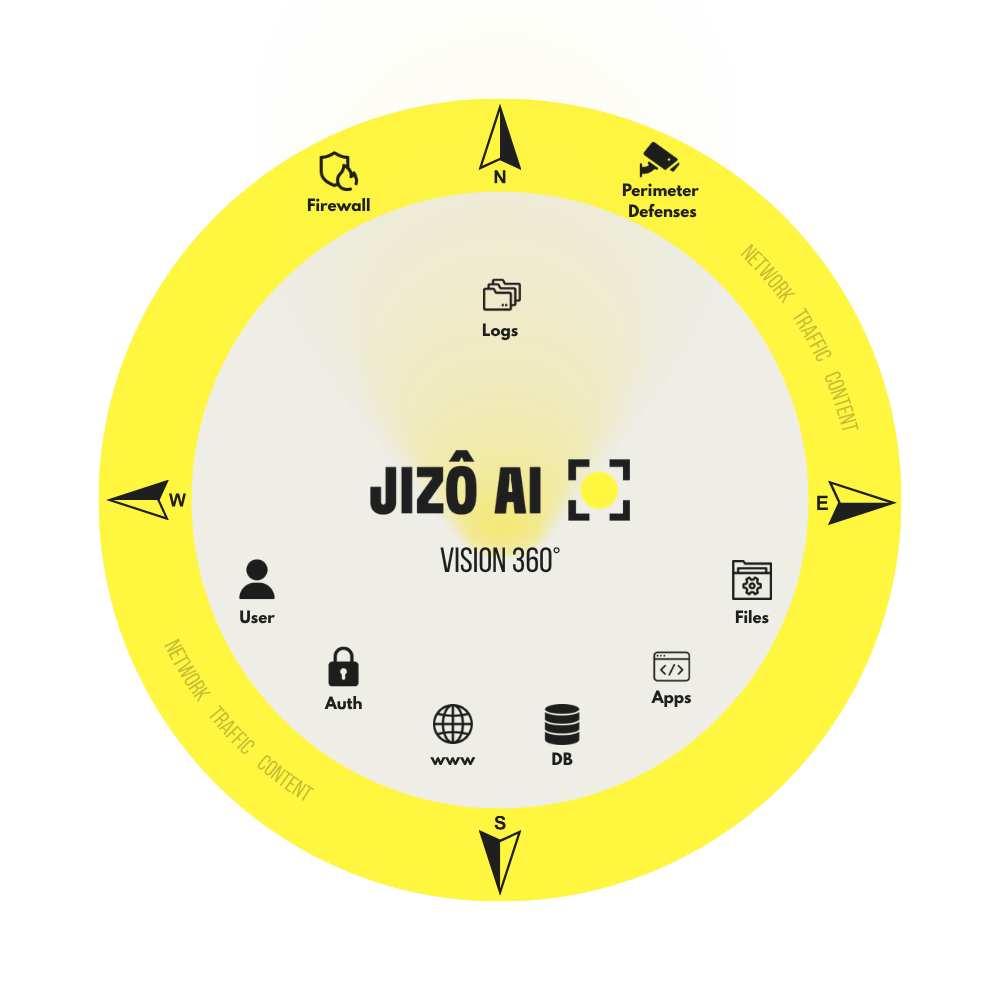
Jizô AI combines behavioral baselines, supervised AI models and MITRE ATT&CK coverage to detect even the most evasive threats, including zero-days, with no prior configuration required.
HOW IT WORKS
LESS NOISE
Incoming signals are automatically aggregated and correlated. Analysts work the queue that matters.
BROADER COVERAGE
Attacks with no known signature are identified by their network behavior, including techniques that will never appear in a vendor catalog.
STEP 3
Every alert comes fully loaded: confidence score, application context, kill chain position. No tab-switching, no manual enrichment.
UNSUPERVISED ML
Jizô AI continuously builds an adaptive behavioral model for your environment, learning what normal looks like, and flagging everything that deviates. It detects threats it has never seen before.
No pre-training, no warm-up period. The platform adapts to your environment as soon as it's deployed.
Anomalous behavior is flagged independently of any known signature, covering the full spectrum of evasion techniques.
Each alert includes a confidence score and a clear rationale. No black box. Analysts make decisions with full causal context.
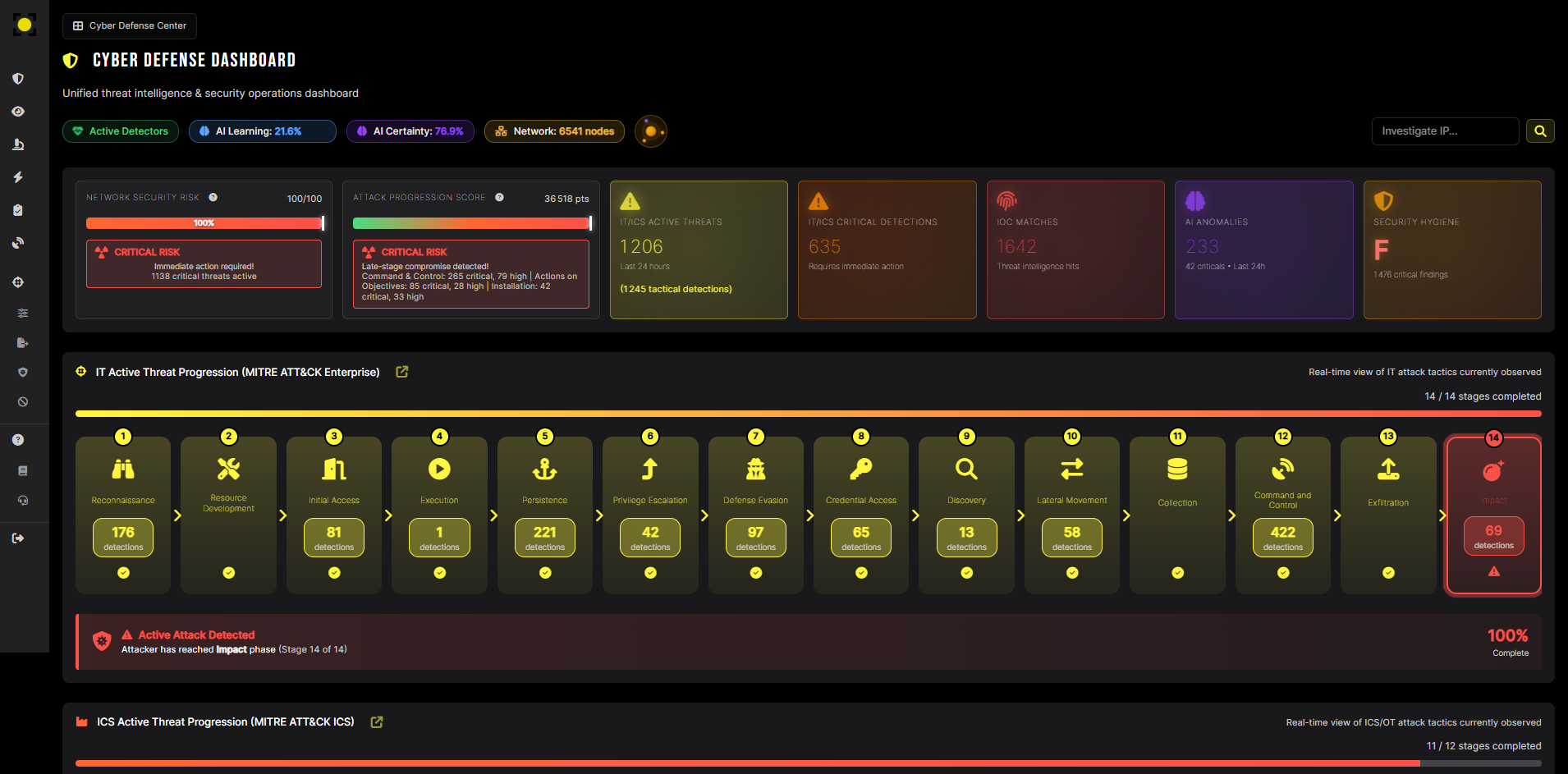
MITRE ATT&CK COVERAGE
Jizô AI covers the full MITRE ATT&CK Enterprise and ICS framework, with kill chain visualization, campaign correlation and a continuously updated detection library.
IT and ICS/OT networks are analyzed in parallel, with no additional tooling or supervision required.
Every attack stage is mapped end-to-end, from initial access to impact. Each step is identified and explained.
Individual detections are correlated over time to surface coordinated attack campaigns and provide a coherent threat picture.
OPERATIONAL CONTEXT
ALERT OVERLOAD
High volumes of low-fidelity alerts with no context or prioritization.
WITH JIZÔ AI
80% fewer alerts, with automatic aggregation, built-in confidence scoring and triage assistance.
SIGNATURELESS THREATS
Advanced techniques bypass traditional detection tools entirely.
WITH JIZÔ AI
Behavioral detection across 130+ MITRE ATT&CK techniques, with or without known signatures.
OT/ICS BLIND SPOTS
Industrial protocols fall outside standard monitoring coverage.
WITH JIZÔ AI
Native IT and OT/ICS coverage, agentless, with zero impact on production systems.
SLOW INVESTIGATION
Context reconstruction requires jumping across multiple consoles and log sources.
WITH JIZÔ AI
Full incident context on-screen in seconds. MTTR reduced to under 41 hours.
LONG TIME-TO-VALUE
Weeks of tuning before the first reliable detection.
WITH JIZÔ AI
Automated deployment in under 30 minutes. Detecting from the first packet.

An ideal gathering of exceptional talents and outstanding experiences!

How AI-driven behavioural detection is redefining network security against contemporary threats?

No more fragmented visibility. Jizô AI launches Jizô-M, the centralized supervision console that transforms N isolated Jizô AI instances into a unified, AI-powered command cockpit.